
Phish Threats Are Evolving. How Smart Users Make Safer Networks
What is the first thing that comes to mind when people think of phish threats and cybersecurity solutions?
Usually, you’ll hear all about firewalls, antivirus, encryption, and other products you can buy that are designed to protect your network. As most cybersecurity companies worth their salt will tell you, a good security plan involves many layers, and those products would undoubtedly be critical players in providing you and your business with protection.
However, one of the most effective (and most commonly overlooked) methods of keeping data safe is arming those who have access to it with knowledge of how to protect it. In the cybersecurity arms race, criminals and security products are continually evolving, which leaves users as one of the weakest links in IT security.
An analogy we like to use is that of protecting a house. You can install an alarm, get a guard dog, and put locks on the windows, but if a homeowner opens the door and welcomes in someone they don’t recognize as being a criminal – well, it’s only a matter of time before their security is compromised.
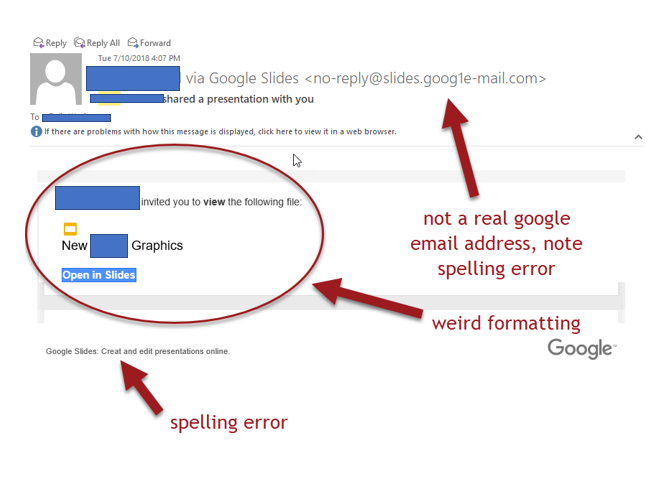
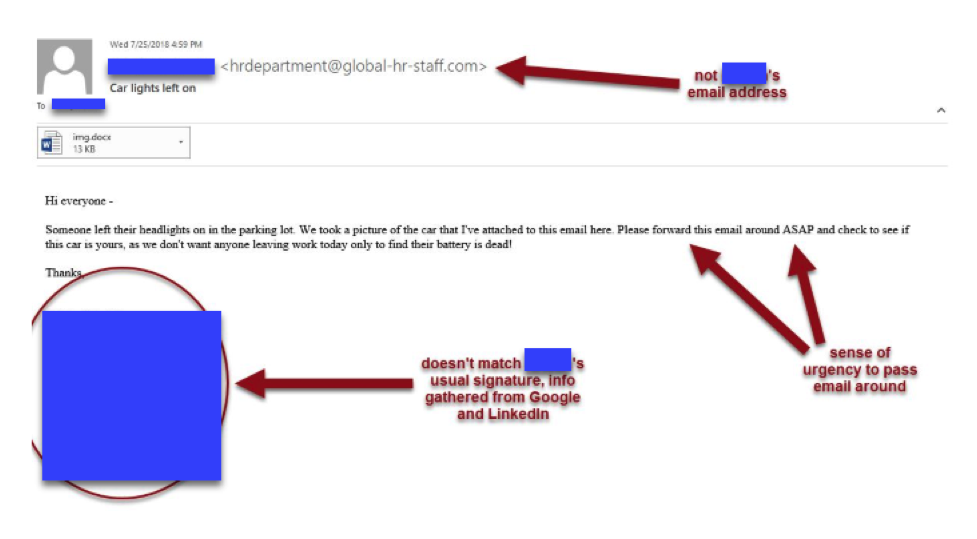
Cybercriminals are becoming increasingly aware of this weakness, and efforts to capitalize on it have gotten more and more sophisticated. We all like to laugh about the classic trope of the Nigerian Prince asking for wire transfer “monies,” but the threat landscape has evolved, and the ability for criminals to craft convincing spear phishing emails is, frankly, frightening.
In a 2018 study, Sophos found that people opened 30% of phishing emails and that 93% of data breaches included a phishing email. Furthermore, 41% of IT professionals reported seeing daily phishing attacks.
There is no doubt that phishing poses a significant threat, and that users are a highly effective attack vector for criminals.
How can this be remedied?
IT security professionals are now recognizing the importance of awareness and education surrounding phishing and cybersecurity.
There are a variety of products, programs, and resources that can aid in training your users. A product that we use at Netcetera and strongly endorse is a simulated training module that sends users fake phishing emails. The emails can vary, from Amazon deals to charity requests to fabricated emails from the CEO. User engagement with these emails can be tracked, recording for example, who opened the email, who tried to download an attachment, and who entered their credentials.
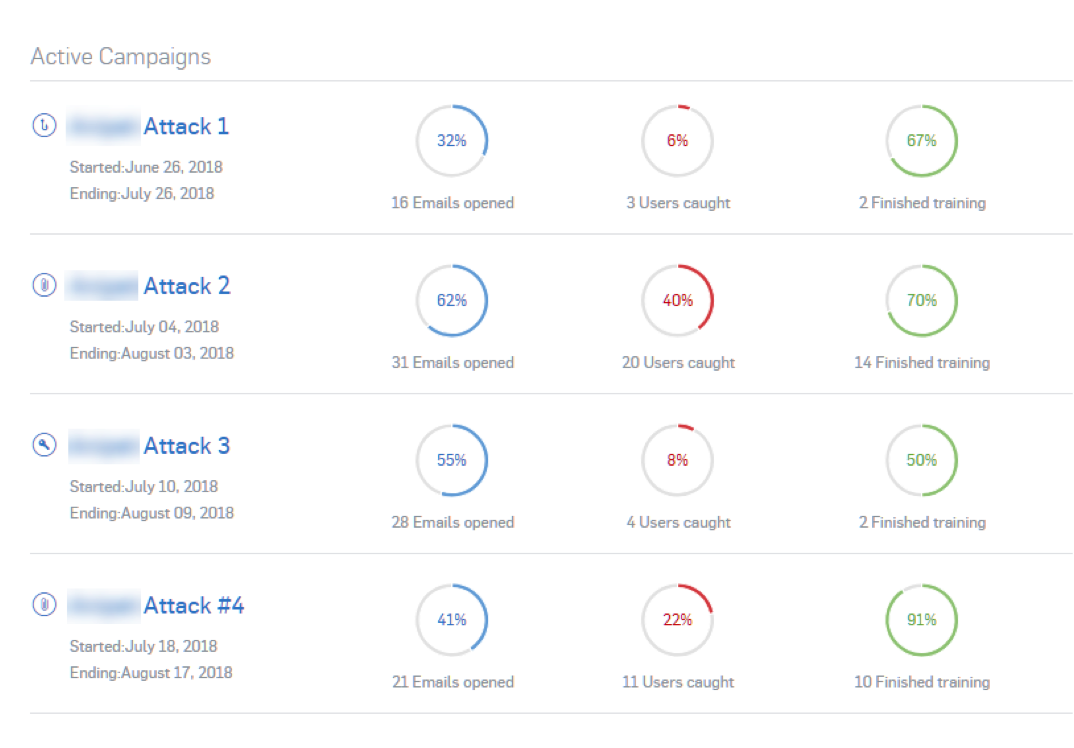
The program we use, Phish Threat, also enrolls those users who demonstrate risky behaviour, into training, and tracks who does – and does not – participate.
Companies are often tempted to buy licenses for these products themselves so that they can run them in-house. Generally, we discourage this. In our experience, running campaigns in-house can start out well, but tends to quickly fizzle out as people get busy and other priorities crop up. In some cases, the quality of the campaigns goes down, and in others, it’s forgotten altogether.
By allowing an outside company to conduct these training programs, the quality is typically far superior. For example, when we conduct these campaigns for our clients, a significant amount of time is spent gathering publicly available information about the company and employees so that the phishing emails crafted are both sophisticated and realistic. We track data collected during these campaigns and draft a personalized, detailed report outlining the findings and recommendations moving forward. We are even able to pinpoint users who might be the most at-risk then provide follow-up training.
We recommend running this program, or whatever programs you might be using through your IT provider, 4-5 times a year to promote vigilance and keep education current.
Ultimately, informing your users and keeping them vigilant is one of the best methods of defence in the ever-evolving arms race between businesses and cybercriminals.
Smart users make safer networks.
Contact us at Netcetera if you have a question about Phish Threat, need advice or are thinking about a technology change. We are always happy to help!


